Microsoft announced on February 9th that they are adding a new controls to Windows 11 22H2 (and beyond) that allow organizations to temporarily turn off new features that are periodically released on top of Windows 11 through Windows updates. On February 28th, they announced that those new features will be delivered in the March Patch Tuesday update on March 14th. And also on February 28th, some of those features shipped as part of the “preview” update, KB5022913, including the new controls to keep new features turned off.
Interestingly, these new features will be off by default if devices are “managed” devices, i.e. those that have WSUS or Windows Update for Business (WUfB) policies applied (interesting because past similar “managed device” checks also looked at the AD/AAD join state, MDM management, etc. to decide a device was “managed”). Whether that is sufficient for your specific environment is something that you would need to analyze. If you want to play it safe, you can always apply the new controls. But you don’t have a lot of time as all devices running Windows 11 22H2 will get these new features in less than two weeks.
So if you want to keep these new features turned off for machines in your environment, you really don’t have much time. To get the new GPO setting, you can get the updated WindowsUpdate.admx and corresponding WindowsUpdate.adml files (found in C:\Windows\PolicyDefinitions) by installing KB5022913 on a computer running Windows 11 22H2 (which could enable the “moment” features, as it did on my AD-joined test VM that did not have WSUS or WUfB policies applied); from there, you can add it to your Group Policy central store to enable you to set the new policy:
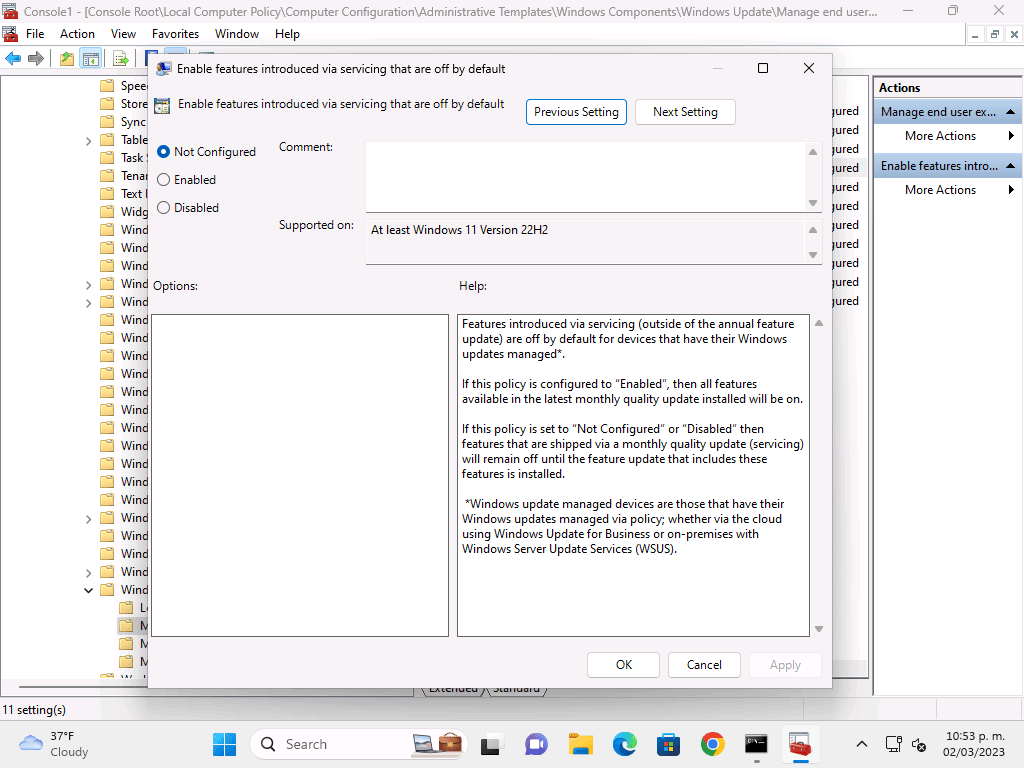
If you set this to “Enabled” the devices will always get new features whether “managed” or not. If you set this to “Disabled” the devices will not get the new features. (The bits may be there, but they won’t be enabled.)
If you are using an MDM service, there is an equivalent MDM policy called AllowTemporaryEnterpriseFeatureControl:
OMA-URI: ./Device/Vendor/MSFT/Policy/Config/Update/AllowTemporaryEnterpriseFeatureControl
Type: int
Setting this to 1 will always enable new “moment” features; setting it to 0 will keep them off.
If you want to set the equivalent directly in the registry, you can do so (where 0 is “keep them off” and 1 is “always turn them on”):
[HKLM\Software\Policies\Microsoft\Windows\WindowsUpdate]
AllowTemporaryEnterpriseFeatureControl=0
If you do prevent them from being enabled, or if that is the default for “managed” machines, when will you get the new features? With the next “feature update” (a name that is now pretty confusing), i.e. when you deploy/install Windows 11 23H2.
The only interesting piece that I haven’t verified yet: What happens for new features that are enabled via new app updates delivered from the Microsoft Store? For example, will you get the updated Notepad app that supports tabs, or will you stay on the current Notepad? Either is possible I suppose.
So the next question then is whether you should enable features or not. In theory, the new features should have minimal impact to the end user, to app compatibility, or much of anything else, but there are always going to be exceptions. For example, apps like Start11 broke with the new update. So there is always some risk. The question is then whether the new functionality justifies that risk. For my personal machines, sure, no problem. For 100,000 PCs at a large enterprise (if they were indeed already running Windows 11 22H2 — more than likely they’re still on Windows 10), that might be too little value for the risk. But at least you have the ability to choose.





One response to “Want to block Windows 11 “moments” that add new features?”
Windows 11 22H2 is incompatible with RADIUS EAP connections that don’t implement TLS 1.3 per Windows 11 22H2 standards. This requires one to workaround the issue or update RADIUS. Is it Microsoft’s goal to drive their customers to the latest everything?
LikeLike