This is one of those topics that I’ve been in the middle of for years. “Can you tell me how to properly wipe a disk before we dispose of or return this PC, following standard X?” where “X” can be one of a few different standards:
- US Department of Defense (DoD) directive 5220.22M
- NIST Special Publication 800-88
- NISPOM Rule
Let’s look at those one at a time, starting with the DoD directive 5220.22M. It’s a big document, but we can focus on one specific portion of it: sanitation (erasing) of data from hard drives (non-removable rigid disks). Obviously physical destruction of the drive (incinerate, pulverize, melt, etc.) is acceptable, but if you want to use the drive again, the basic clearing method is to write over each byte of the drive with a character (e.g. 0x00), its complement (e.g. 0xFF), and then a random character, for a total of three write passes across the whole drive.
This three-pass erasing of the drive was designed to address two problems: (1) there could be deleted-but-not-erased files present on currently-unused portions of the disk, and (2) there could be magnetic “echoes” that could still be used to determine recent bit values even if they were overwritten by new data. The first is still a real issue, but the second is probably no longer an issue. And that’s without considering that SSDs now store data much differently in order to extend the life of the drive by ensuring all bits of the SSD are written an equal number of times (separating logical sectors from their physical storage).
Interestingly, the DoD published an instruction that cancelled directive 5220.22M. Instead, it directs you to NISPOM, which has a different clearing suggestion for “non-removable rigid disks” (gotta love that modern terminology). Instead of three passes, it now suggests a single pass is fine, writing a character (e.g. 0x00) to every location on the media.
So what does NIS 800-88 say? It says “a single overwrite pass with a fixed pattern such as binary zeros typically hinders recovery of data even if state of the art laboratory techniques are applied to attempt to retrieve the data.” Great, that’s in line with NISPOM. But section 2.4 of this document goes much further, talking about issues with this approach (and most of this was written prior to SSDs even being commonplace). It suggests using cryptographic encryption (CE) — basically, encrypt the data but then throw away the encryption keys so that it can’t be decrypted. The suggested method involves self-encrypting drives, but I would argue that software-based encryption (e.g. something like BitLocker) should also be sufficient. Whether anyone has ever gotten someone to sign off on that approach is a question left to others.
Personally, I think all of these documents are long-winded, out-of-date, and in general need of significant re-writes given how much technology has changed since they were first written (going back to the late 1990’s). But that’s not my battle to fight.
But what about a tool to do the recommended three-pass overwrite?
Even though that’s not actually a DoD recommendation any more, customers still ask for it, and if customers still ask for it, you can bet that there are a number of companies out there that sell tools that explicitly quote 5220.22M, 800-88, NISPOM, etc., as well as a variety of other similar international and industry-specific standards.
What about free tools? There is a cipher.exe utility in Windows that has been around for close to 20 years that can do this, but there isn’t much information available about how it actually works, nor is there much control over it (point it at an empty drive and it will erase all unallocated space, which would be all of it). We thought about adding that into BDD/MDT, but never got around to it.
There is also a GNU open source utility called shred available (and it’s been around as long as some of these standards). The source code for that, along with documentation, tells you exactly how it works. It supports up to 25 passes, using a variety of different bit patterns as well as random data. If you’re really determined and have time to kill, run it with all 25 if you’d like, even though one is probably enough. This one is easy to use from Linux (install it using your favorite package manager), and there is an old Windows port around (not that I actually tried it).
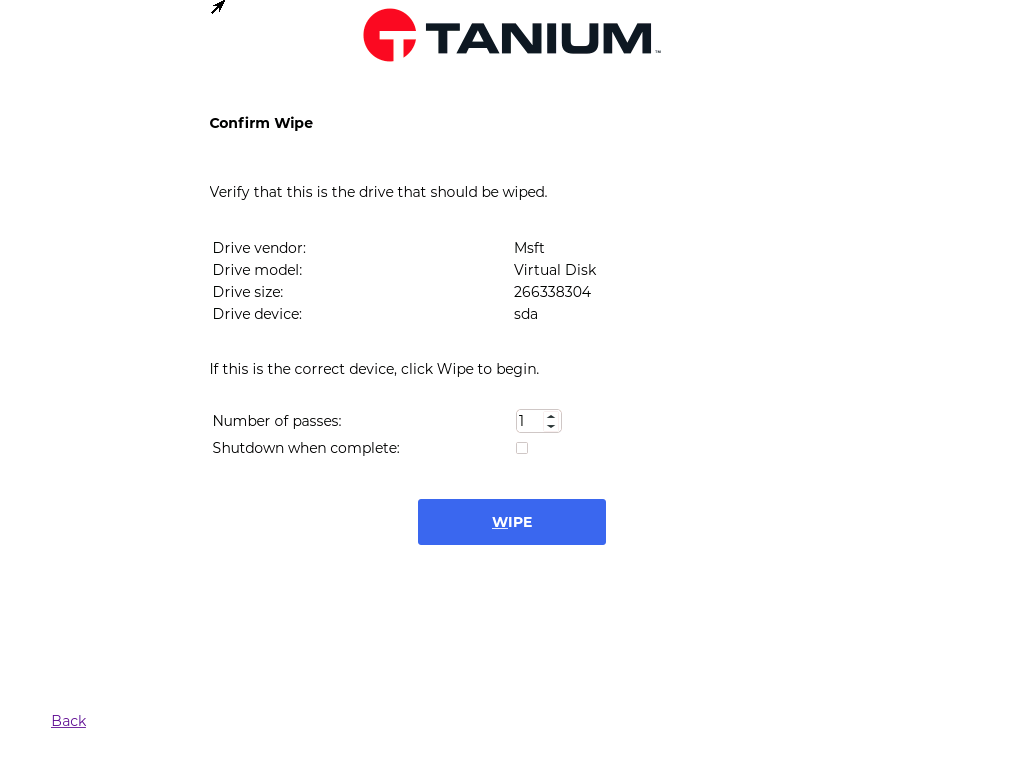
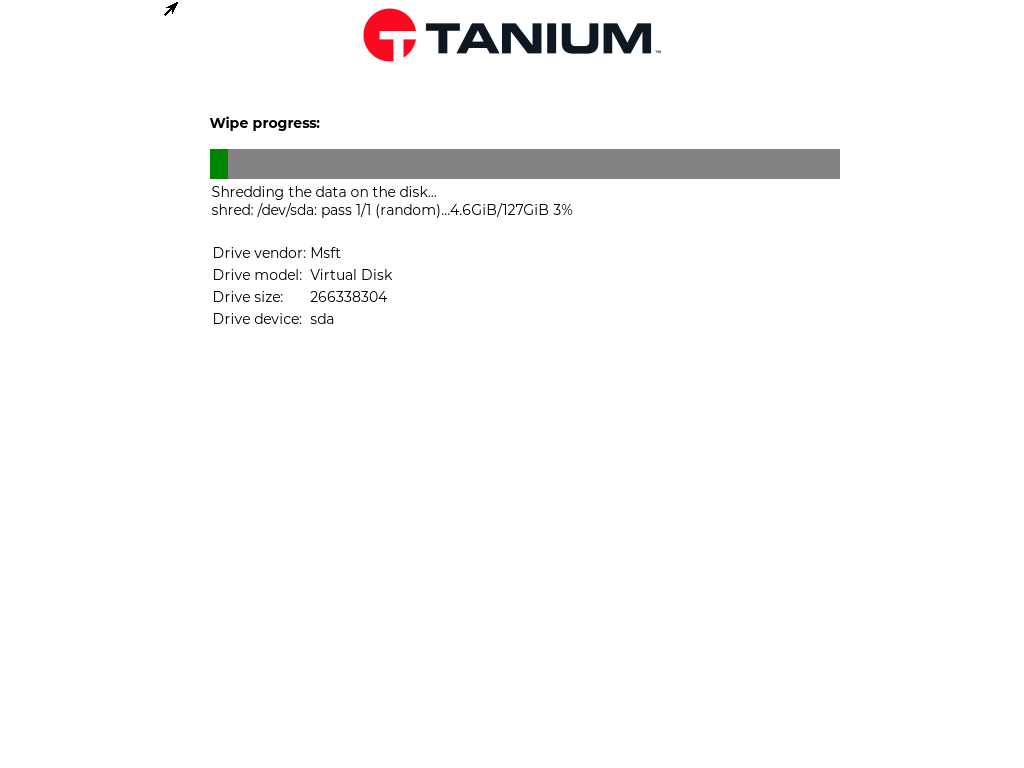
We built a feature into Tanium Provision to run shred with as many passes as you like, displaying progress as it goes along:
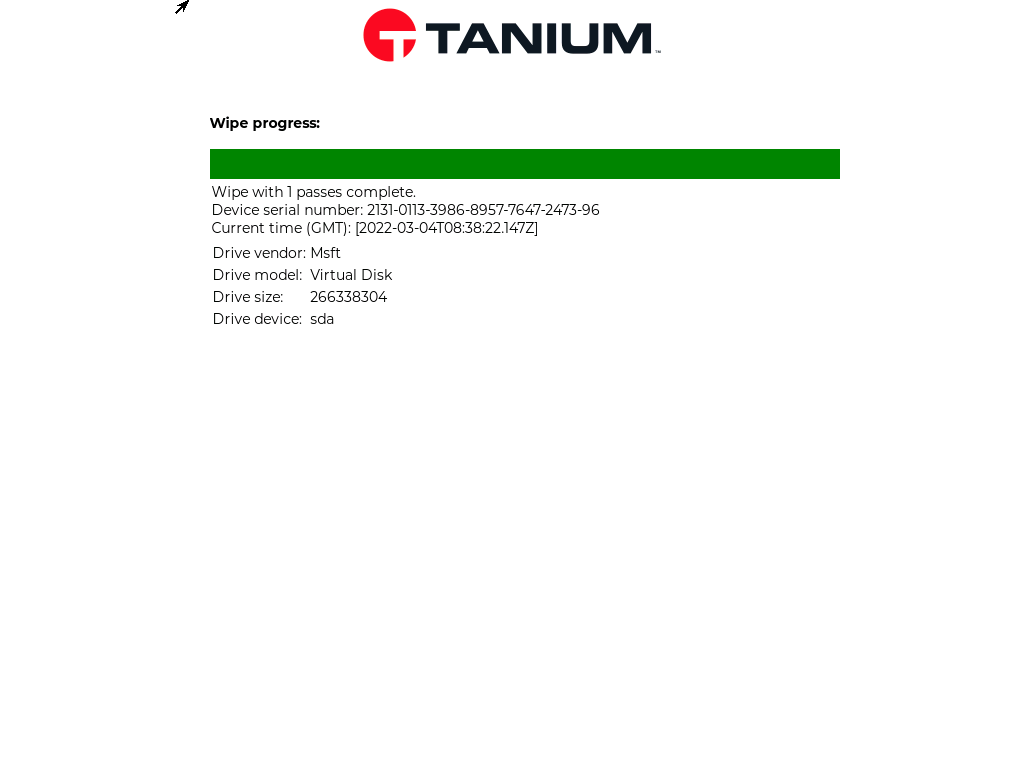
I’m firmly in the “one pass is enough” crowd, but if you really want more, go for it.





2 responses to “Do you properly wipe your disks (maybe following US government standards)?”
you mention cipher.exe, would you say sdelete.exe would perform the same way and meet standards with a multiple pass process?
LikeLike
From reading the docs, it does sound like it would meet the requirements (although there’s still a question as to whether that’s really effective with SSDs).
LikeLike