I posted a blog a back in March that talked about a new “-online” option that I added to the Get-WindowsAutopilotInfo script which will grab the hardware hash from a device and add it to Windows Autopilot using the Graph API. I’ve made some further enhancements to that process to provide a few additional options. Here’s the PowerShell syntax view:
Get-WindowsAutoPilotInfo.ps1 [[-Name] <String[]>] [-OutputFile <String>] [-GroupTag <String>]
[-Append] [-Credential <PSCredential>] [-Partner] [-Force] [-Online] [-AddToGroup <String>] [-Assign]
There are two new parameters designed to be used in combination with the existing “-Online” switch. From the help:
-Online [<SwitchParameter>]
Add computers to Windows Autopilot via the Intune Graph API-AddToGroup <String>
Specifies the name of the Azure AD group that the new device should be added to.-Assign [<SwitchParameter>]
Wait for the Autopilot profile assignment. (This can take a while for dynamic groups.)
So as an example, if you specify something like this:
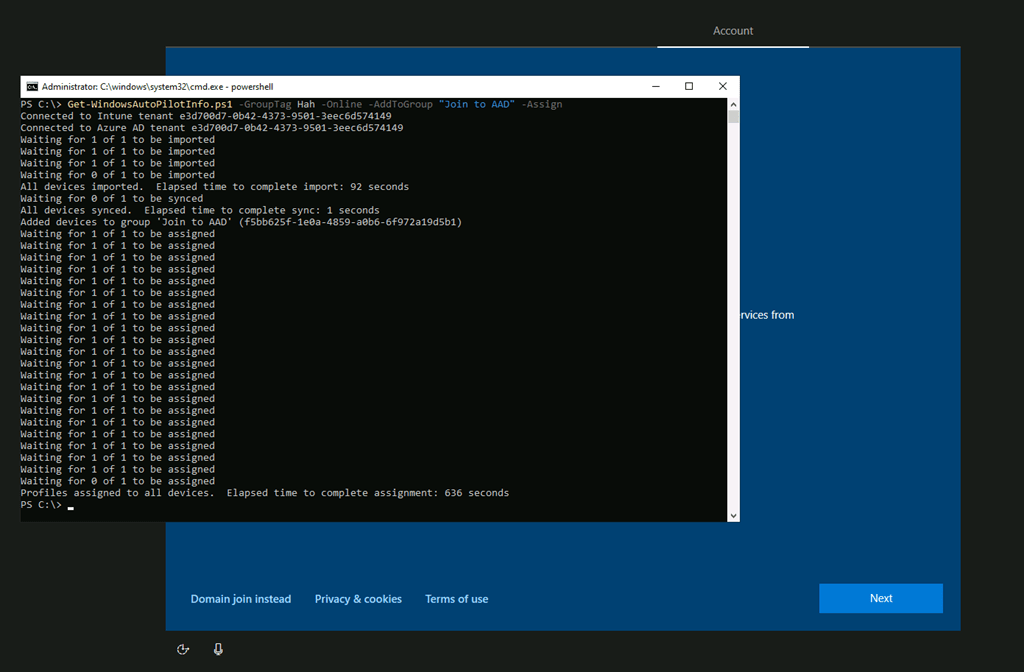
here’s what the result would be:
- From “-Online”:
- The device will be registered in the tenant that you specify. (The script will prompt for an account and password with sufficient rights to Intune, then use the Graph API to add the device.)
- It will wait to confirm that the device was registered and that it is present in Intune (synced back automatically by Intune using a delta sync process after the import completes).
- From “-AddToGroup”:
- It will add the new device’s Azure AD computer object into the group name that you specify.
- From “-Assign”:
- It will then wait for Intune to assign an Autopilot profile to the device.
Here’s an example:

As you can see, it took about 1.5 minutes to register the device via Graph API, almost no time for the device to sync back to Intune (done automatically as part of the import process), and then about 10.5 minutes to assign the Autopilot profile that was tied to the group that I specified. (If you leave off the “-AddToGroup” and instead leverage an Azure AD dynamic group, e.g. one based on the group tag, it will likely take longer because you have to wait for Azure AD to update the group membership.)
If you then wanted to deploy the machine using Autopilot, you can reboot the machine using “shutdown /r /t 0” to initiate the reboot so the device downloads the newly-assigned Autopilot profile. If you are using white glove, you don’t need the reboot (but you do need to use a networking trick so this is done from an appropriate point in OOBE).
For those of you who have implemented any sort of similar process for doing “just-in-time” device registration, note that you don’t need to use the “Invoke-AutopilotSync” cmdlet to perform a sync (or the equivalent by clicking the “Sync” button from the Autopilot device list in the Intune portal), and in fact we recommend that you don’t because it performs a full sync that can actually slow down the process. As you can see in my example above, the automatic delta sync that is performed after the device is imported and completes quickly.
Also, if you are defining group tags solely for the purpose of getting devices into the right groups, you might consider this as an “eliminate the middle-man” alternative: Don’t assign a group tag in order to enable a dynamic group to pick up the device based on the group tag, instead just put the device into the group directly.





6 responses to “Automating the Windows Autopilot device hash import and profile assignment process”
This is awesome! Our IT org has been following your blog for a while now. My scripts have been doing the exact things you describe here (using dynamic groups based on group tag, and waiting for profile assignment before finishing script execution). These changes will simplify the scripts a ton. Thanks Michael!
LikeLiked by 1 person
I get problems when running the script with the group options, insufficient privileges. Do we need to give permissions for the Graph api?
LikeLike
Yes, definitely the script requires opting in to use the modules, as well as permissions to the underlying objects.
LikeLiked by 2 people
Thanks for this great job!
Is it possible to automatically authenticate securely with the -online parameter using a runbook or something else?
In our area, the people who install through autopilot don’t have an intune account.
I think that can affect a lot of customers.
LikeLike
There are solutions out there where people have built web services to do this sort of thing: A script uploads the hardware hash to blob storage, a runbook/service grabs the hashes from blob storage and adds them via Intune Graph API. So the end result is the same, just a different process to get to that result.
LikeLike
Thanks Michael for sharing your knowledge and scripts. Anyone else getting 502 (bad gateway) errors when using Get-WindowsAutoPilotInfo in “-online” mode since Monday August 3rd? I’m seeing the 502 error after “Added devices to group…”. It happens after a random number of “Waiting for X of Y to be assigned” messages have been printed, so I assume that the 502 error is in response to a call to Get-AutopilotDevice.
LikeLike