I mentioned in my previous blog about the WindowsAutopilotIntune module that I had switched the module over to using the Microsoft.Graph.Intune module so that the same authentication logic could be used across the Intune and Autopilot modules. Coincidentally, someone at the same time asked how to get that module to connect to an Intune tenant that was different from the user account that was authenticating. For example, I should be able to access the Intune tenant for contosocm.onmicrosoft.com using an account from autopilotrocks.onmicrosoft.com. The question is, how? Fortunately, when I have questions like that I ping people like David Falkus, and even after doing that several times, he still replies to my queries.
So let’s walk through the process.
Step #1: Creating a guest account
In order for an Azure Active Directory account from one tenant to be able to do anything related to another tenant, it will need to be added as a guest to that tenant. So, I need to add my Michael@AutopilotRocks.com account as a guest to my contosocm.onmicrosoft.com tenant. I can sign into the https://devicemanagement.microsoft.com portal, where I can navigate to the Users blade, and from there I can click the “+ New Guest User” link.

Then you can specify the user to invite:

Make sure you scroll down to see the additional settings. In this case, I made the user an Intune Administrator:

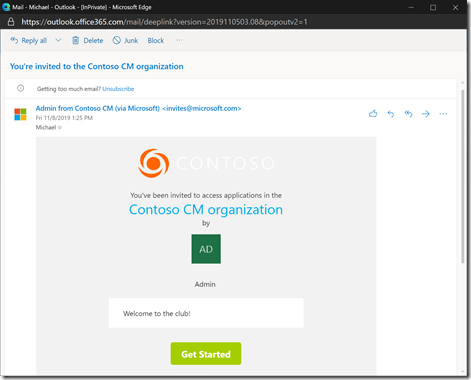
Once you click “Invite” an e-mail will be sent to the user:
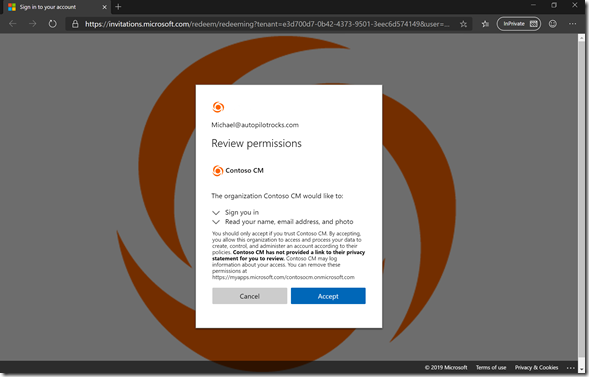
After clicking “Get Started” you will need to accept the permissions:
After doing that, I can sign into https://devicemanagement.microsoft.com and click “Switch directory” to access the newly-granted tenant:
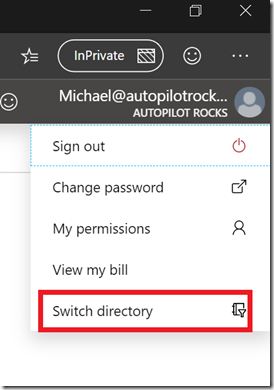
You should see it in the list:
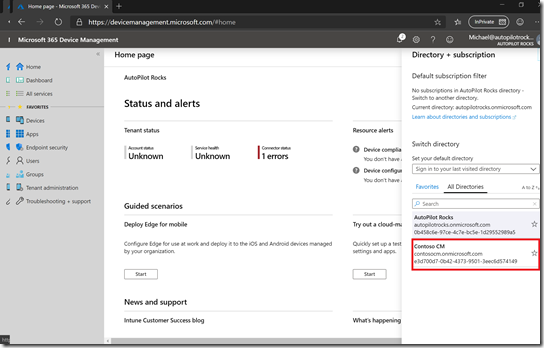
Clicking on it will change to that directory. Then you can see that you are signed into one directory and administering another one:

Once there, you can navigate to any of the Intune blades, confirming that you do indeed have Intune Admin rights. So that confirms our guest user is set up correctly.
Step #2: Authenticate to the Graph API
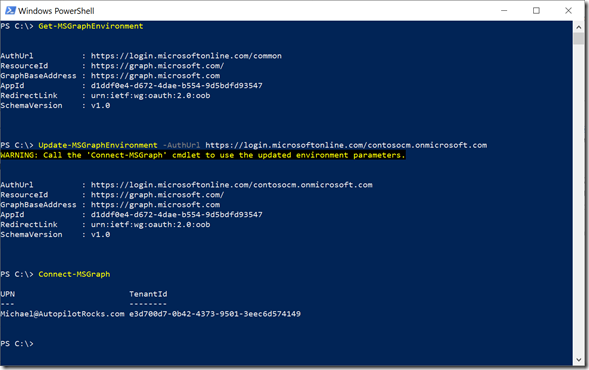
If I open a PowerShell session (where I’ve already installed the Microsoft.Graph.Intune module), I can authenticate with the Microsoft Graph using the Connect-MSGraph cmdlet. But that will by default authenticate to the tenant that the device belongs to. The tenant GUID here is for the autopilotrocks.onmicrosoft.com tenant.

So how do I force the cmdlet to authenticate to something else? I need to explicitly configure it.
While the most logical way of doing something like this would be via the Connect-MSGraph parameters, that’s not the way this one works. Instead, you have to modify the URLs that it uses by default. You can see these using the Get-MSGraphEnvironment cmdlet:

Notice the AuthUrl value includes /common at the end of it? That says to use the same tenant as the user account. If you want to use something else, you need to change that value using the Update-MSGraphEnvironment cmdlet:

And of course, it doesn’t work.
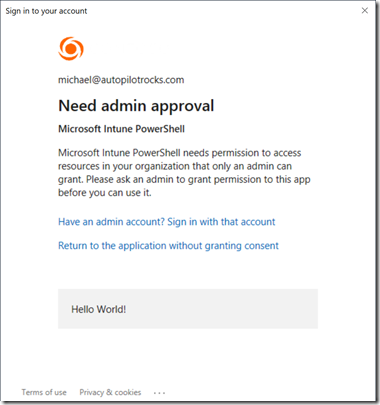
To get past that, you need to run “Connect-MSGraph –AdminConsent” command once. Then the guest user will be able to sign in successfully.
Using something like this, it would be feasible to copy objects from one tenant to another. For example, you could sign into one tenant, grab an Autopilot profile object and save it to a variable, then sign into a different tenant and create a new profile from that variable. Of course that requires the cmdlets to support pulling all the properties from the pipeline, which I don’t think they’ll do right now, but that’s easy to fix (when I get some time). I suspect the Intune cmdlets already support that.





3 responses to “Multi-tenant Intune Graph API usage via PowerShell”
Sorry for cross posting but you fido topic does not allow replies. When will come support for locking the workstation when removing the key? Even enabling the GPO and starting the removal smartcard service does not lock the system when the key is removes.
LikeLike
WordPress shuts off comments after 30 days – seems like a reasonable default, mainly guarding against spammers. I don’t know if this policy would work, but it’s worth a try: https://docs.microsoft.com/en-us/windows/security/threat-protection/security-policy-settings/interactive-logon-smart-card-removal-behavior
LikeLike
Hi Michael, i tried the CSP and also the local GPO policy but still no lock after removing the yubikey 😦
LikeLike