Back in July, Alex Simons announced the public preview of Azure Active Directory’s support for FIDO2 security keys. Even though I have been carrying one of those around with me for several months waiting for that (I couldn’t come up with a good reason to ask for access to the private preview), it’s taken me a little while to get around to trying it out. There’s no time like the present.
Step #1: Set up the key
Following through the instructions in that blog, the first step is to enable FIDO2 as an authentication mechanism in an Azure AD tenant. Navigating in the Azure portal to Azure Active Directory –> Authentication Methods, I can see the new FIDO2 security key option:
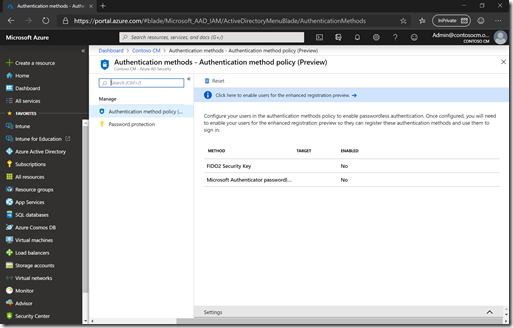
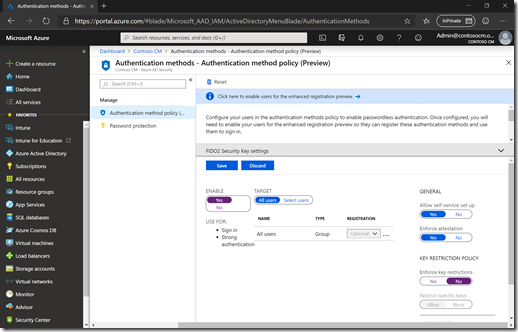
After clicking on the FIDO2 security key method, I can enable it. I’ll do nice and easy and turn it on for everyone in my tenant, and allow any key to be used:
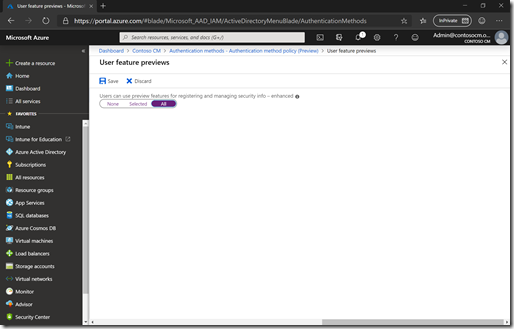
And as mentioned in the text at the top of the page, I also need to enable the enhanced registration preview, which I’ll also do for all users:
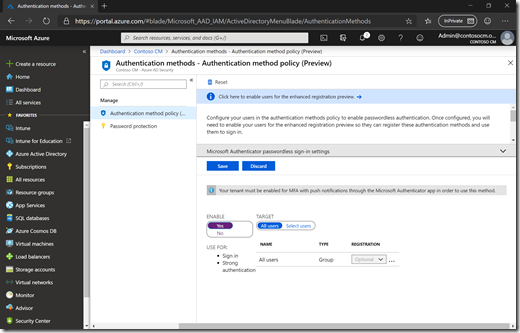
Since I was already using the Microsoft Authenticator app, I also enabled that:
The next step is for an end user to complete. As documented in the My Profile (preview) user documentation, you can get to this via https://myprofile.microsoft.com.
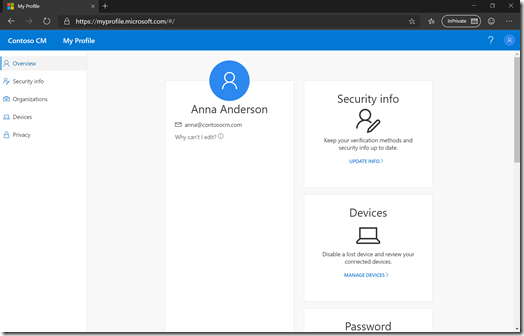
From there, I can click on Update Info in the Security Info box, or from the left-hand list. After I complete the Microsoft Authenticator MFA request (which I had previously enabled for this account), it takes me to the page that the blog referenced:
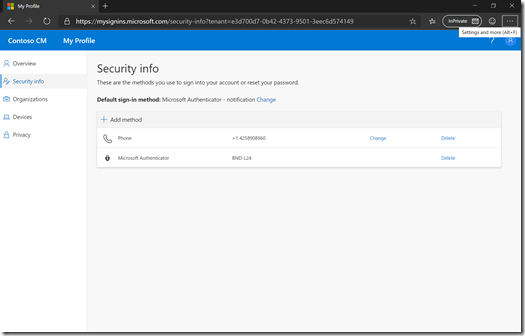
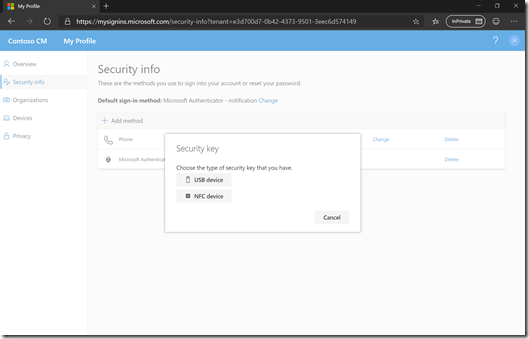
From there I can click “+ Add method” and choose “Security key” in the list:
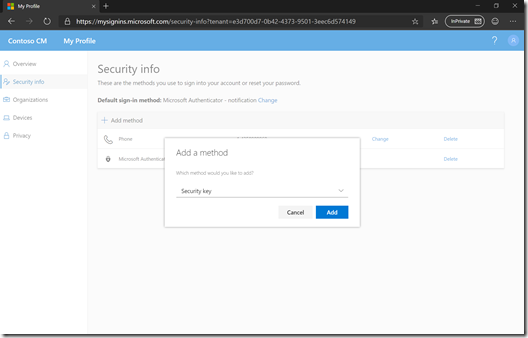
I have a USB device (this little device from Yubikey), so I’ll choose that option:
Time to get ready:
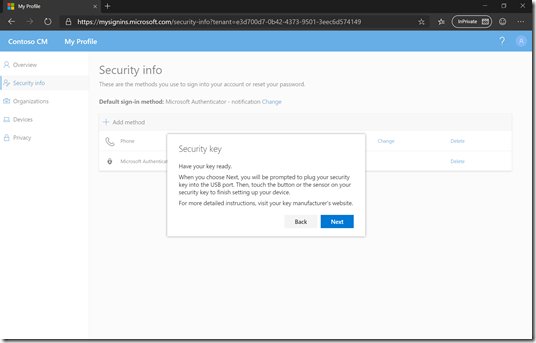
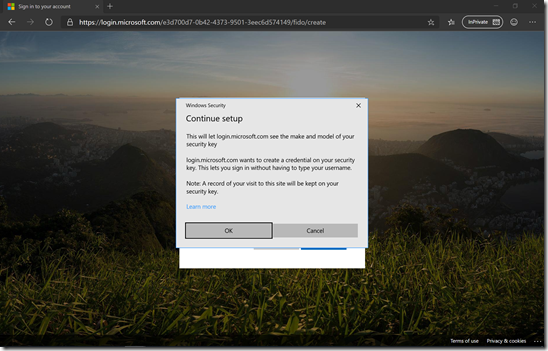
I’m then redirected to an Azure AD sign-in page, which prompts to set up my security key:
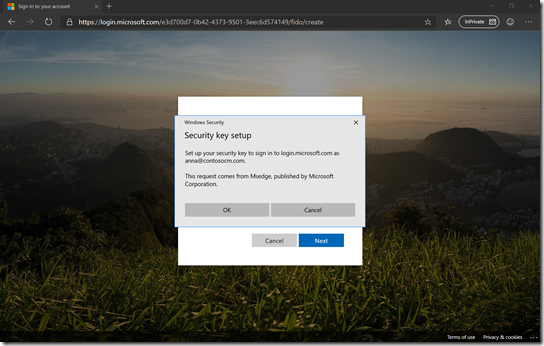
One more prompt:
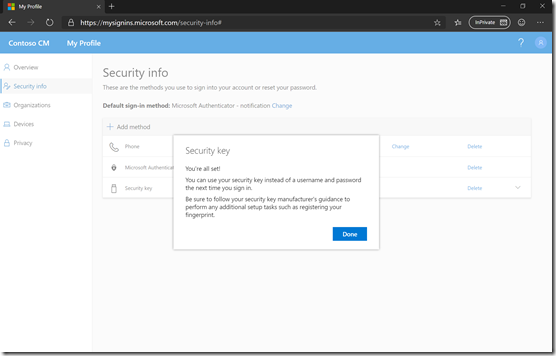
After inserting my key, providing a PIN, and then pressing the button on the FIDO2 key, I’m then redirected back to the https://mysignins.microsoft.com website (completing another Microsoft Authenticator MFA sequence) where I have to give my FIDO2 key a name:
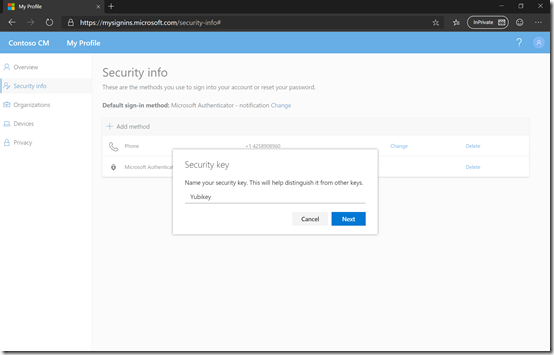
And presto, I’m all set:
To try it out, I opened a new InPrivate window in the Microsoft Edge beta (my normal day-to-day browser, which works extremely well). I then went back to https://myprofile.microsoft.com. I didn’t see the security option initially:
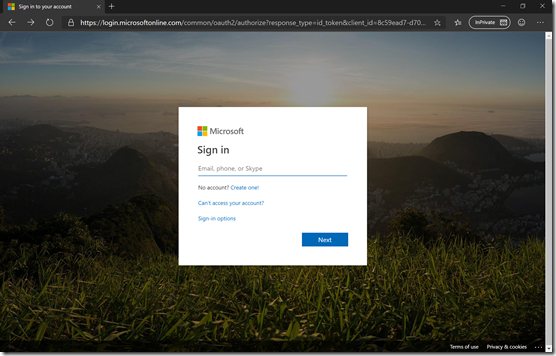
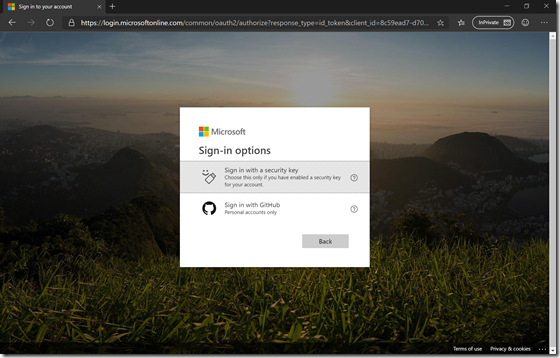
But clicking on Sign-in options gave me the choice:
When choosing that option, I first need to provide the PIN for my FIDO2 key:
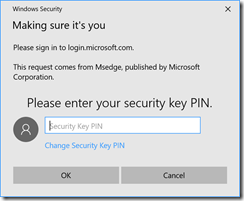
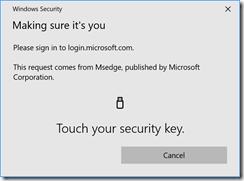
and then I am prompted to push the button:
And I’m done. No need to type in my e-mail address (username/UPN) or password, no MFA prompt, just a PIN and a button push. (And that’s in an InPrivate browser session on my laptop, which is joined into a different Azure AD tenant.)
Step #2: Use the key to sign into Windows 10
The next step is to enable the use of a FIDO2 key to sign into Windows 10. As documented in the Azure AD documentation, this requires applying a policy via Intune to enable a credential provider. This is available in the Windows Hello for Business enrollment properties:
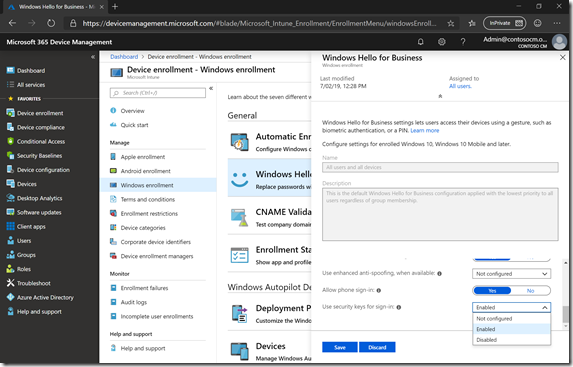
That is a global setting though (and doesn’t require Windows Hello for Business, even though the setting is in the list with Hello). If you want to turn it on for a smaller group, you can create a device configuration profile that sets the same thing:
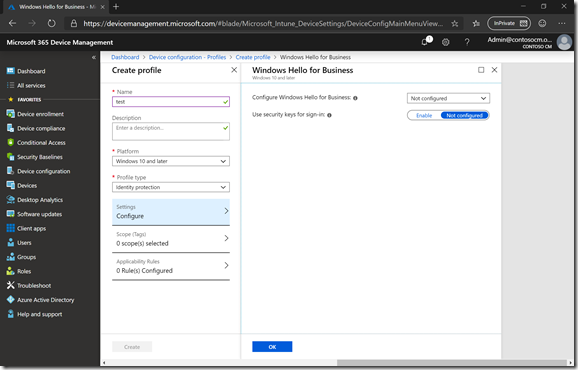
The same doc above says you need to use a custom OMA-URI for doing this, but that’s obviously no longer true.
So what’s the result? I was too lazy to do proper screen captures (from a physical machine so I could use the USB key), so you’ll have to live with my photos of the screen. First, you can see the new security key option:
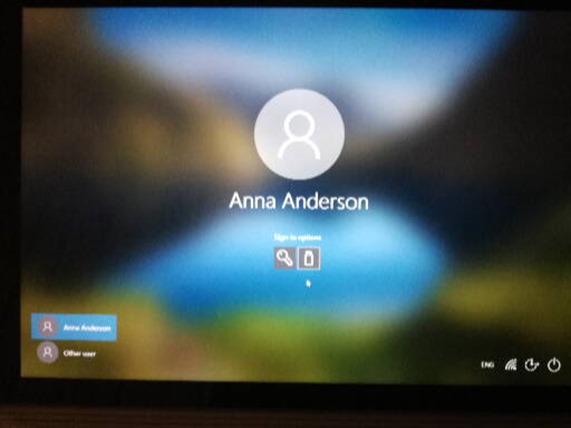
Next, when I insert the FIDO2 key, I get prompted to enter my PIN:
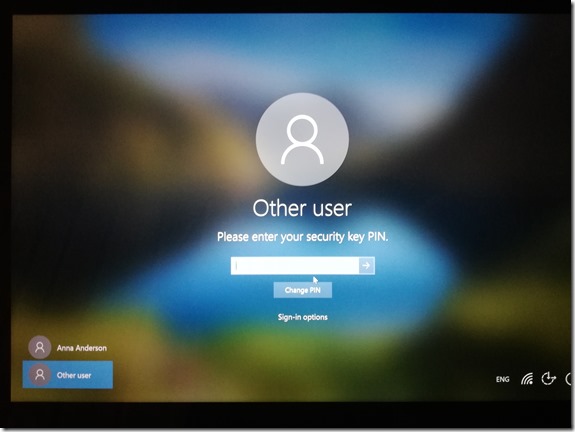
And then, to press the button on the key:

And presto, the sign-in is complete – overall, it works quite well.
Step #3: Still a work-in-progress
There’s one more piece that we can’t yet do: use the FIDO2 key to complete the initial Azure AD authentication that starts the Windows Autopilot process. The support for doing this isn’t yet available in OOBE. So you still have to do the initial authentication for Azure AD Join using an e-mail address and password, but then you can switch to the FIDO2 key for subsequent logons. So close…





2 responses to “Sign in to Azure Active Directory with a FIDO2 key”
Is the sign in to windows only working for a full cloud solution? What if we access on-prem resources with NTLM/IWA (on a aad joined device) ? Will sign in to windows also work for hybrid aad joined devices? Will it also work for AD joined devices? if so what are the requirement? Last question i have if we enable all the requirements are users forced to use passwordless auth or will username password still work and be default?
LikeLike
From https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-authentication-passwordless-security-key, “security keys only work for Azure Active Directory Joined machines for now.” Enabling these options doesn’t prevent using passwords, and right now I see no way to prevent the use of passwords.
LikeLike