Some customers have asked “how do I delegate access to manage Windows Autopilot devices in Intune.” Well, Intune has a robust Role-Based Access Control (RBAC) mechanism that can be used to create a role that can do that – and only that. You just need to understand what needs to be granted to that role. While the documentation isn’t particularly helpful in telling you that (this doc appears to be the best overview), you can at least see what’s needed in the console itself. So navigate to the All Roles list. I’ll give you a hint to start your explanation: The built-in Policy and Profile Manager role has all the needed rights (and then some). So let’s look at the list of permissions on that role:

So which would be your guess? If you understand Windows Autopilot, Apple School Manager, etc., you should understand that they are enrollment programs. Look at the detailed permissions (all of which are selected for this role):
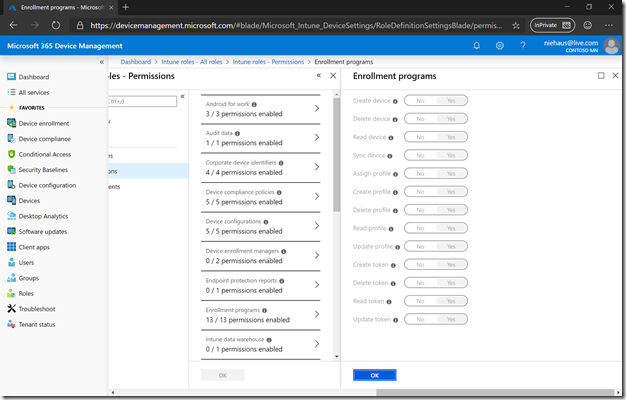
If you hover over the info icon, it will give you more info on each of these. And you can see that the permissions are shared (e.g. giving rights for an Autopilot operation may also provide rights for similar Apple operations). Alas, not all of the tips are complete, so you might not know which are applicable to Windows Autopilot. But logically, the first nine would apply; the last four are Apple-specific and not used with Windows Autopilot.
So, let’s create a custom role. Go back to the “All roles” list and click the “+ Add” button. Give the new role a name, such as “Autopilot Operator.” Click on “Permissions” to see the list:
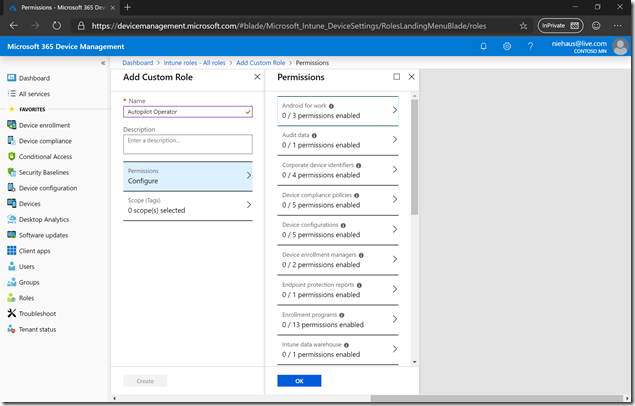
And then select “Enrollment programs” to see the individual rights. Select the first nine in the list:
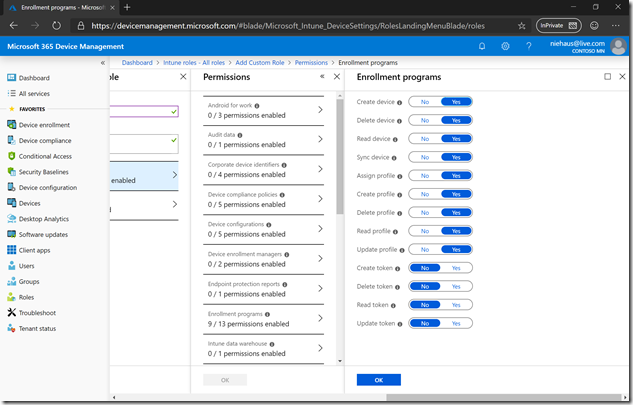
Then click OK twice and Create to create the custom role:

Now you just need to assign that role to a user. Click on the role and then “Assignments”:
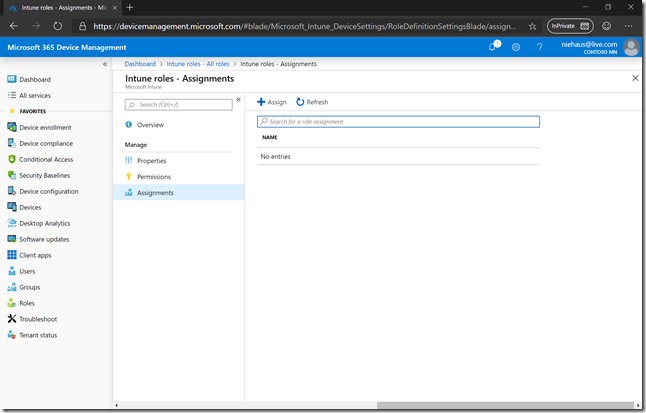
You don’t assign users directly to roles. Instead, you assign a role to one or more groups, then members of that group are granted the rights for the role. So, click to “Assign” then “Add” then select a group.
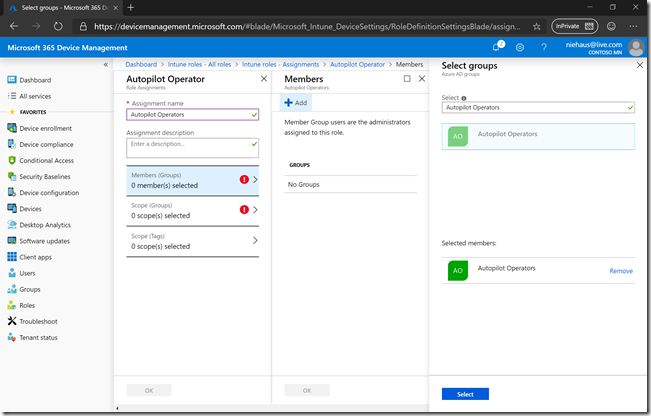
Then click Select and then OK. You then need to specify the scope. It’s easiest to specify “All devices”:
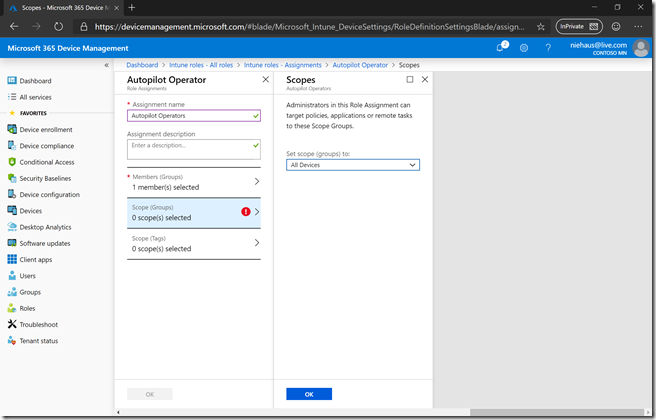
Click OK twice and then assignment is complete. To try it out, sign in as a user who is a member of the group that was assigned the role, and verify that user can indeed work with Autopilot devices and profiles. And guess what? It doesn’t work:
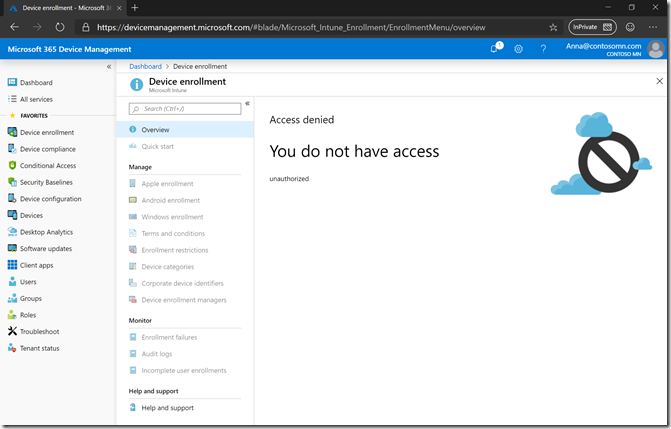
OK, so obviously there are more permissions required. After comparing the permissions in the built-in Policy and Profile Manager role, I first tried adding read access to the “Organization” class. That improved things a little, but still no luck. Next up, I tried to add read access to “Audit data.” And that was enough. So I guess those two are required.

One last tidbit: When signed into Intune, you can navigate to the “My permissions” node under Roles to see the specific rights that you have (unless you are an admin, then it just tells you that). And you can see the rights that this role provides:

Notice the names? These are the “internal” resource names.





One response to “Creating a Windows Autopilot role in Intune”
Thank you for this post; it was very helpful. We had created a role like this in the past but it would still not allow users to see data and upload CSVs because these two last permissions were missing.
LikeLike