Here’s an easy one to try. In Azure AD, you can enable an option to require MFA before a user can join a device to Azure AD:
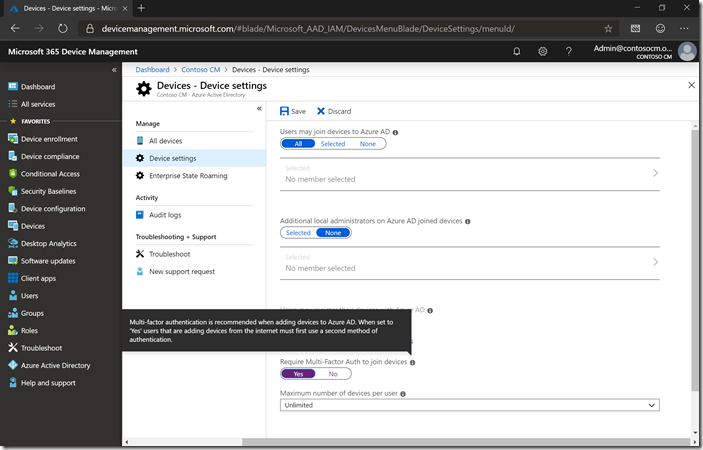
When not using ADFS or an external federation provider (the Azure AD team now recommends passthrough or password hash authentication), turning that to “Yes” will result in an additional dialog after the user types in their e-mail address (UPN) and password. And if they’ve never set up MFA, they can do it right there, setting up the Microsoft Authenticator. To make things a little more challenging, I set up a new user (and assigned an EMS license to them), which also means their password is expired and must be changed on first use. Here’s what that flow looks like:
First, type in your e-mail address (UPN).

Then, specify your (expired) password.

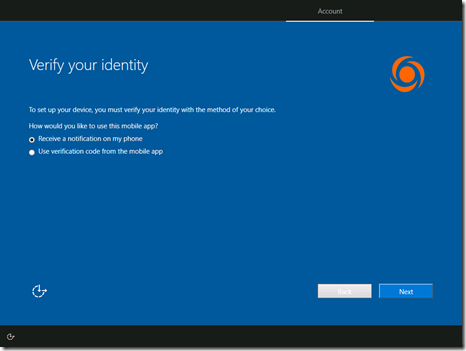
Next, the MFA setup starts for the new user.

I prefer the Microsoft Authenticator app, but there are other options available too.

Then specify to do the verification using the Authenticator app.
Then respond to the notification.

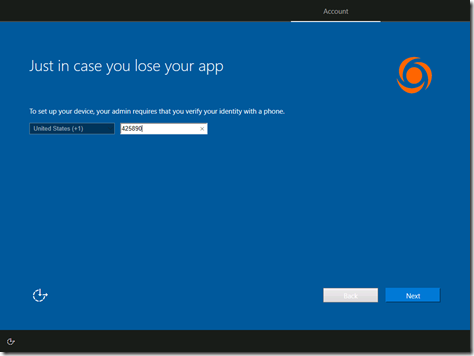
Put in your cell phone number, just in case (for recovery purposes).
And finally, change your password.

That’s a smooth process.