Some organizations want to display a “terms of use” page to users when the join or enroll in the organization. (Personally, I think this is a bit silly, but if it makes the lawyers happy…) I always knew that could be enabled in Intune:

with some simple text fields that can be displayed to the end user for them to accept. You also then specify the URL in the MDM enrollment settings to make that happen during OOBE:
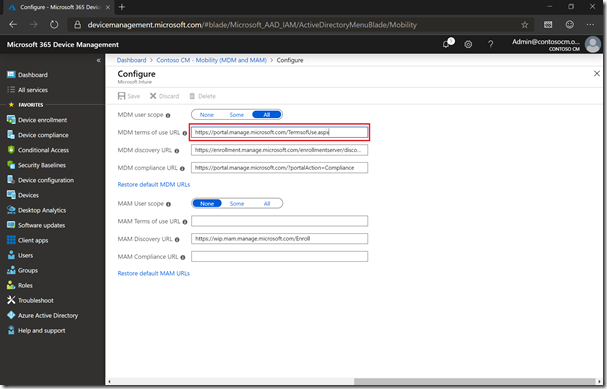
(And FYI, if a user ever tries to enroll a device and gets an error that points to the terms of use URL returning an unexpected HTTP response, that probably means you are using the default Intune URL and haven’t assigned an Intune license to the user.)
But I noticed when looking at the terms of use settings in Intune that there is a link that I hadn’t seen before:
That points to an October 2018 blog post (migrated since then to the Tech Community website) that talks about a new Azure AD terms of use feature which has more capabilities: support for PDF files, localized versions, integration with Conditional Access, etc. That post then points to the Azure AD documentation page that describes how to set it up. So, I tried it, first deleting the Intune terms of use and then creating a new Azure AD Terms of Use policy with an (obnoxious) 7-page PDF file for the policy:

That’s the easy (and safe) part. Next, you need to create a conditional access policy. I am a conditional access neophyte (still teaching myself all the Intune features, and I’m not sure I’ll ever finish that task), so I’m fairly cautious (as I’ve seen the customer support calls from customers that have locked themselves out of their entire tenants). But if scoped to a limited set of users, you can at least limit the harm. So here’s what I set up:
First, limit the impact to a group of users. (I also excluded Global Administrators, just in case.)
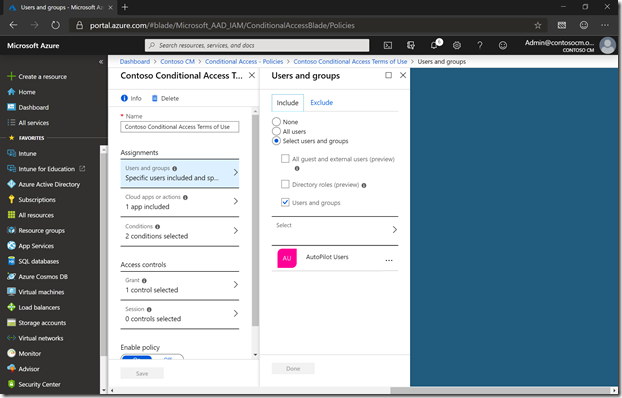
Then, only affect the Microsoft Intune Enrollment app.

And only for Windows.

Grant access based on Contoso Terms of Use.

And that policy was then enabled. And here’s the results, seen after putting in the user’s e-mail address (UPN) and password:

Pretty (although I still think it’s silly).